
Most people don't think twice about sharing their phone number, but if you think about it, your phone number is a great jumping off point for anyone who wants to steal from you. You use your it for banking, receiving two-factor authentication codes, and even just logging into social media.
If you’re wondering what someone can do with your phone number, the answer is nuanced. It opens the door for attackers, but it’s not a problem as long as you have safeguards in place.
An attacker can’t gain access to your device with just a phone number. But, if they combine it with other information from a database breach, or publicly available records the risks increase. They can use it as part of a phishing campaign or account takeover, and in a worst-case scenario, identity theft.
What you need to know:
- A phone number alone cannot directly hack your device.
- Scammers use phone numbers for phishing, impersonation, and account reset attempts.
- The most serious risk is SIM swapping, which allows interception of login codes.
- Risk increases when your number is combined with other leaked personal data.
- Unexpected service issues or login alerts can signal trouble.
- Strong authentication and carrier protections significantly reduce risk.
What can scammers do with your phone number?
Scammers who obtain your phone number can use it to launch phishing texts, spoof your caller ID, and attempt password resets on your accounts. In many cases, your phone number is one cog of a broader strategy to defraud you. What’s worth noting here is that none of these attacks require physical access to your device. Your number alone is enough to start.
There are several common tactics that scammers employ, the most common of which is smishing. These are SMS-based phishing messages that impersonate companies you often deal with, such as banks, delivery services, and government agencies. The messages most often have a link to a web page with a form that requires you to fill in your information, or it will prompt you to call a fake support line. These texts look like they come from an official source, and so people will respond before they’ve even had a second thought.
In some cases, your number may be used to trigger a password reset. It’s standard practice for online services to send a one-time code via SMS when users request a reset. If this happens, and the attacker already knows your email address, they can initiate the reset and then try to intercept or use social engineering to get that code from you.
Can scammers access your accounts with just your number?
A phone number alone is usually not enough to gain direct access to your accounts. For an attack to be successful, they will need at least one other piece of information, such as your email address or a leaked password.
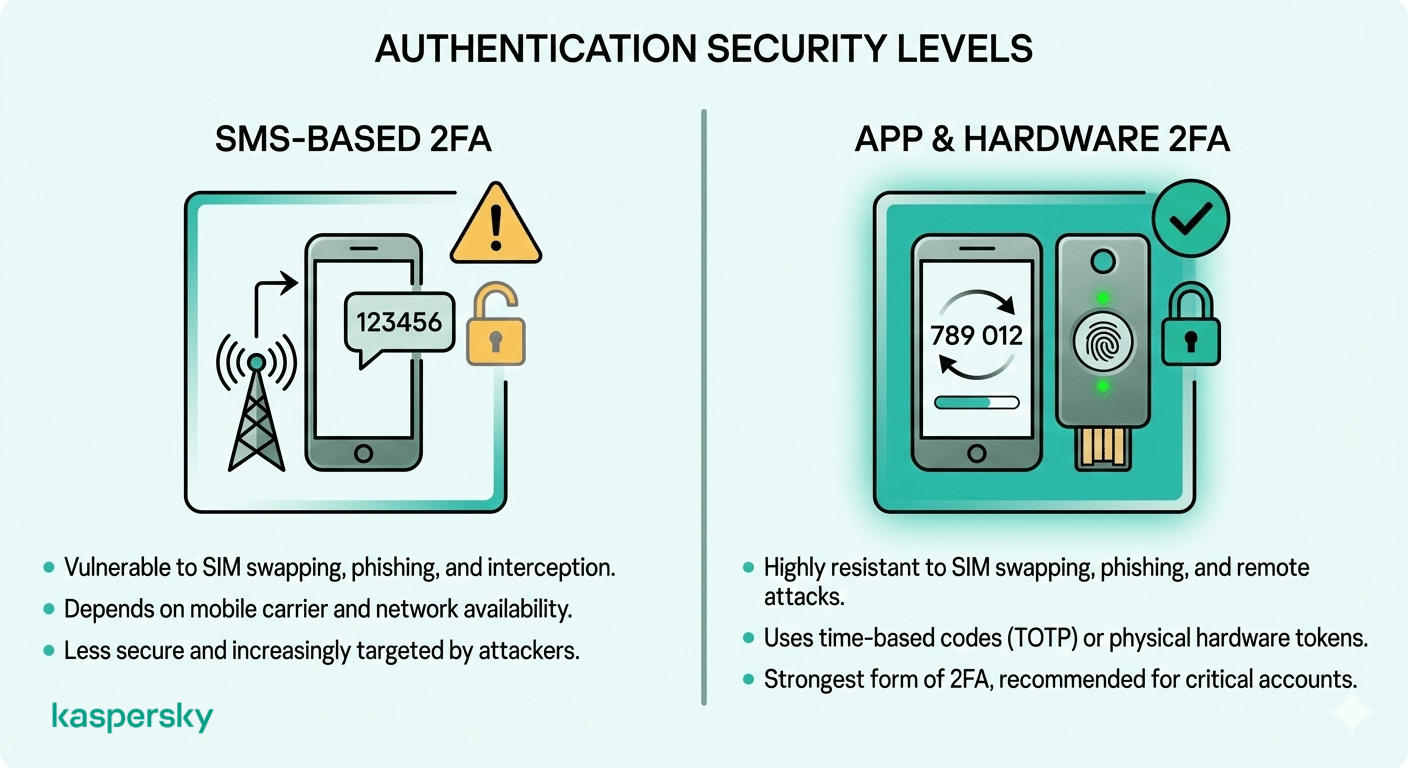
The main vulnerability lies in the password reset process. If a service you’re registered for uses SMS-based verification as its only recovery option, and an attacker can receive your text messages, they can access your account. This would require the attacker to have gained access to your messages through SIM swapping or malware on your device.
Most companies are moving away from SMS as a second factor for any sensitive information transfer because it happens so often. There are several high-profile documented account takeovers that include cryptocurrency holders, journalists and more.
Protect Against Phone Scammers
Kaspersky Premium helps monitor for data leaks, detect suspicious account activity, and strengthen protection against SIM swap–related account takeovers.
Try Premium for FreeCan scammers impersonate you or target your contacts?
Yes, caller ID spoofing lets an attacker make calls or send texts that appear to come from your number. This approach has become even more widespread with advances in AI technology that make it easier to impersonate you. This technology is widely available, costs next to nothing, and is easy to use.
Once a spammer has spoofed your number, they can call your contacts and request emergency money transfers, send fake payment links, or request verification codes. It’s easy to see why these attacks succeed: your contact sees a name they trust on their screen, why wouldn’t they follow through on your request?
When you learn that someone is spoofing your number, let your contacts know immediately. Use a channel that you control (either a group message from your device or an email), and report the incident to your carrier.
Can your number be used for identity theft?
A phone number on its own isn’t enough for identity theft. It becomes a problem when combined with other personally identifiable information (PII), whether it’s your full name, date of birth, or Social Security number. When an attacker has two or more data points, they can try to open credit card accounts in your name, file fraudulent tax returns, or access your financial accounts.
The problem for end users is knowing how much of your information is already available. There are often large-scale data breaches where millions of phone numbers are leaked, alongside client names, addresses and account details.
These records can end up on the dark web, where attackers can buy them as part of a database. For this reason, many companies treat phone numbers as sensitive data; once it’s used in conjunction with other personal data, the information sensitivity of a number goes up dramatically. And, in most cases, that exposure didn’t come from something you did wrong.
How do scammers get your phone number in the first place?
Scammers acquire phone numbers through data breaches, people-search websites, phishing forms, and automated dialing systems that detect active lines. Keep in mind, there is often a long time, sometimes years, between your number being compromised and you noticing suspicious activity.
If you’re wondering how scammers get your phone number, it almost always comes back to one of these sources.
The other source that scammers use to get phone numbers is public records. Court filings, voter registrations, and property records often include phone numbers and are freely available online in many jurisdictions. Filling out a warranty registration card or entering a store loyalty program can feed your number into marketing databases that are later breached or resold.
What role do data breaches and data brokers play?
Data breaches are the largest source of leaked phone numbers, and data brokers add fuel to the fire by making information from the breaches widely available.
When a company suffers a breach, customer records often surface on dark web forums and marketplaces within days. From there, attackers cross-reference them against existing databases to assemble an increasingly complete profile of each person on the list.
Data brokers like Whitepages, Spokeo and BeenVerified compound the problem of data breaches by aggregating public and commercial data into a searchable database. From there, for a small fee, anyone can look up your phone number and get back the name, address and other personal details linked to that number. It is possible to remove your information from these sites, but you’ll have to email each broker individually to send an opt-out request.
How can you tell if your phone number is compromised?
Your phone number may be compromised when you suddenly lose cellular service or receive password reset messages you didn’t request. Other signs include notifications about account changes you didn’t make and reports from contacts that they’ve received suspicious messages from your number.
Watch for a cluster of these events within a short period. A single spam call is not cause for concern. The perfect storm is a complete loss of signal, despite your device and SIM card being physically undamaged, coupled with login alerts or authentication requests you didn't trigger. This pattern typically points to a SIM swap.
If anything looks suspicious, do a quick recon of your carrier account for unauthorized edits. Call from a different phone or visit a store in person. Then log in to your email, banking, and social media accounts to check for changes you didn't make.
What is a SIM swap and why is it the biggest threat?
A SIM swap is an attack where a scammer successfully convinces your mobile carrier to transfer your phone number to a SIM card they control. This allows the scammer to intercept all calls and text messages sent to your number. It is the most serious phone-number-based threat as it bypasses the safety mechanism of SMS-based two-factor authentication entirely.
If a SIM swap is successful, the attacker can receive every SMS verification code sent to your phone. Think of all the possible instances where this could happen: one-time passwords for email and banking, cryptocurrency exchange verification, and social media access.
The damage can escalate quickly when your email account is compromised, as the scammer can initiate password resets across dozens of other services. To help users, the FCC’s SIM swap scam advisory covers carrier-level protections and reporting steps, as well as how it works and what to watch for.
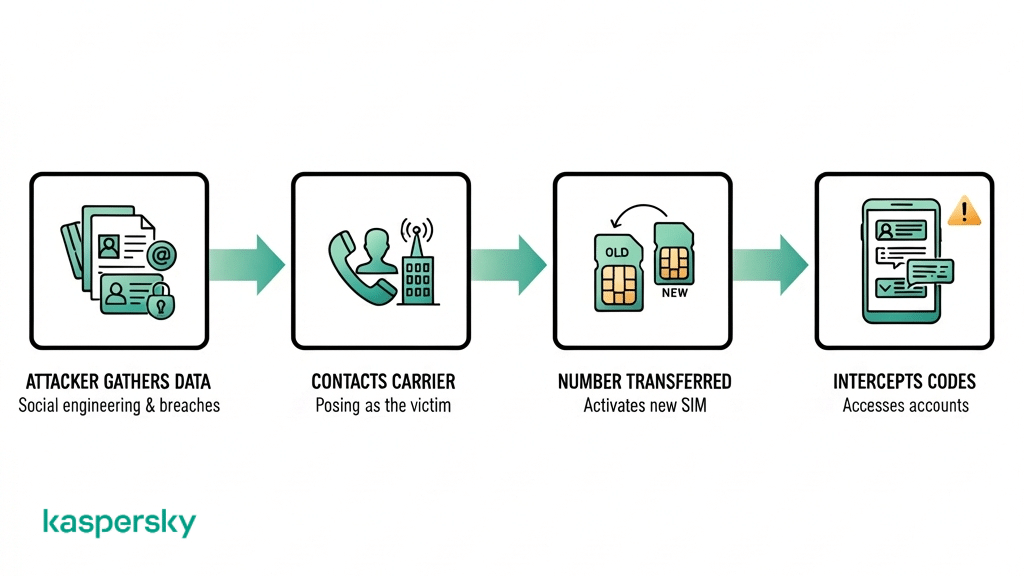
How does a SIM swap work?
For a SIM swap to work successfully, the attacker will first gather personal information about the target, then pose as you and contact the carrier to transfer your number.
The attacker collects information such as name, address, account number, last four digits of a Social Security number from prior data breaches or social media profiles. The attacker will then initiate the SIM swap with the carrier via the online portal or support line. Because they are in possession of your information, they are able to successfully complete the verification process and the transfer is approved.
In some cases, the attacks involve bribing or socially engineering carrier employees directly. A variant of SIM swapping, called port-out fraud, follows a similar process, but transfers the number to a different carrier.
Scammers like SIM swaps because any attack that reroutes SMS messages instantly bypasses the security of every account that depends on SMS verification codes.
Should you be worried if someone has your phone number?
If someone has your phone number, it’s not something to worry about just yet. You’ll likely get spam calls and the occasional phishing text, but that alone isn’t cause for concern; your accounts or identity aren’t in danger.
There is a higher level of risk when you use your number for SMS-based account recovery (for email, banking or other accounts). And the risk increases if your phone number has been exposed with other personal data in a breach. When a phone number hacker has your email and a leaked password, they have a lot more to work with than someone who found your number on social media.
What is normal spam versus a serious threat?
Normal spam is a scattershot approach that consists of robocalls, telemarketing, and generic scam texts that are sent to thousands of numbers at once. These are annoying although unlikely to be dangerous, and the only actions you need to take are blocking and reporting them.
In comparison, serious threats tend to be targeted messages with your real name, alongside your bank, or recent transactions that suggest the sender has more than just your number. Repeated password reset codes are a signal that someone is actively trying to access your accounts. In the case of a SIM swap, your phone might suddenly show “No Service”.
What should you do if a scammer has your phone number?
If you believe a scammer has your phone number, you need to immediately lock your carrier account, change the passwords on your most important accounts, and upgrade your authentication methods. You should also report the incident.
This should all be done as quickly as possible because the time between a SIM swap and full account takeover can take as little as a few minutes. Knowing what to do if a scammer has your phone number comes down to speed.
If you’re unsure what to do if a hacker has your phone number, start by securing your carrier account. Use a different phone (a land line or a family member’s), or visit a physical store, and request that they immediately put a freeze on SIM changes and port-out requests.
Once your account is secure, check your email accounts first (since they control resets for everything else), then banking, then social media. If you are worried that you have been a victim of identity theft, freeze your credit with all three bureaus (Equifax, Experian, TransUnion) and file a report at IdentityTheft.gov.
When you file the report, make sure you document everything in as much detail as you can. Include screenshots, timestamps, and reference numbers from carrier calls, as you may need to dispute fraudulent charges at a later stage.
How do you secure your carrier account?
To secure your carrier account, you should set a SIM PIN, create a strong, unique account passcode and enable number transfer protections.
A SIM PIN is a code that needs to be entered successfully before your SIM card can be used in a new device. You can set this up in your phone’s settings or by calling support. In addition, your carrier account (where you log in for billing) needs to have a strong passcode that’s different from your SIM PIN.
Lastly, most carriers have the option for a number lock or port freeze to prevent unauthorized transfers. You can enable these settings in your online account. For a comprehensive overview of mobile security, NIST’s mobile device security recommendations provide a useful framework that covers most eventualities.
How do you secure your online accounts?
Replace SMS-based two-factor authentication with an app-based or hardware-based alternative. Use an authenticator app like Google Authenticator, Microsoft Authenticator, or Authy to generate time-based codes on your device, this will make your accounts immune to SIM swap attacks.
To further secure your important accounts, you could use a hardware security key like a YubiKey. These make remote account takeovers impossible because they require physical possession of the key to authorize a login.
Reusing passwords also makes your accounts more vulnerable because if one website you use is hacked, the attacker then has your password to access several other sites where you have an account. To reduce this risk, use a password manager to generate and store unique passwords for every account.
For stronger protection, set up multi-factor authentication using an app-based or hardware-based method instead of SMS. This approach keeps your verification codes tied to your device rather than your phone number, making it significantly harder for attackers to intercept them.
How can you protect your phone number long term?
To protect your phone number long term, the goal is to reduce where it is exposed and minimize its role in your account security. Unfortunately, it’s not a one-time fix, and something that you may have to do a few times a year.
Start by removing your number wherever it’s listed online. This includes your social media accounts, and business directories. You may also need to opt out of data broker sites, either manually using opt-out requests or using a service like DeleteMe.
Then, draw up a list of accounts that use your phone number for recovery, and move them to app-based authentication.
For an extra layer of security, you can opt for a secondary number with a prepaid SIM or a VoIP service to use when you sign up for food delivery apps and retail accounts. This is a number you can easily swap out if it is compromised.
Review your privacy settings regularly as platform defaults can shift after updates. A profile field that was once private may quietly become public. Understanding what info someone can get from your phone number makes it easier to decide which details to lock down and which to remove entirely. This only needs to take 10 minutes every quarter, but will prevent a lot of cleanup down the line. Consider using a comprehensive security solution like Kaspersky Premium to monitor for data leaks involving your personal information, including your phone number.
Related Articles:
- How can I effectively prevent SIM swapping attacks?
- How can you protect yourself from Mobile Scams?
- What are the risks associated with Smishing attacks?
- How can you enhance your Mobile Phone Security today?
Related Products:
FAQs
Can someone track my location with my phone number?
No, location tracking through a phone number requires either access to carrier-level infrastructure or the installation of spyware on your device. Location tracking is restricted to law enforcement with a warrant. There are scam websites that offer phone-number-based tracking, these are almost always phishing traps or fraud.
Can someone access my bank account with my phone number?
A phone number on its own is not enough to access your bank account. However, if it is combined with other personal information, it could be used to carry out a SIM swap. That would allow an attacker to intercept SMS verification codes and potentially gain access to your accounts.
Should I change my phone number after identity theft?
No, it only makes sense to change your phone number after identity theft if you are the victim of a SIM swap or harassment. Most vulnerabilities are solved by securing your carrier account, upgrading authentication, and freezing your credit. The FTC’s identity theft recovery steps can help guide your decision.

